5 Best Tips to Improve WooCommerce Security

Everyone needs to improve WooCommerce security if they’re running a WooCommerce website. WooCommerce websites are a particularly tantalizing target for hackers. Once they gain control of a WooCommerce site, they can steal customer data, redirect your site’s URLs to other eCommerce sites of their choosing, and generally wreak all kinds of havoc. Here are 5 things you can do right now to avoid being hacked.
1. Get the Best Hosting to Instantly Improve WooCommerce Security
The very first thing to do to improve WooCommerce security is to obtain the best hosting you can find. Shared hosting on the cheapest plan from a low-tier provider is the worst way to go.
A big (and overlooked) problem with almost all WordPress hosts, shared or not, is that your website directories are often wide open to attack. That’s because they require a certain degree of write-ability to install plugins and themes and allow them to write to caching directories and such.
There are lots of articles that show technical IT people how to lock everything down, but these are points of failure you don’t want to have to deal with if something goes wrong or you’re not sure how to do it.
Instead, pick a web hosting company like Pantheon.io. They’ve thought of all of this stuff in advance and designed their hosting from the ground up in a next-generation way.
For example, Pantheon gives you development and test site environments to add your plugins and themes and try out various things and make mistakes on. When your code is ready to go live, you push it to the live site. Pantheon always locks the live site down by making all but the uploads directory read-only.
The vast majority of plugins have no problem working on Pantheon because many write to a common “cache” directory that Pantheon’s Valhalla file system already provides. Any plugins that need other kinds of write access can have it through symlink shortcuts you (or Pantheon Support) can set up that point to Pantheon’s separate “files” directory. That directory lives on a separate, optimized server (which is also where all your media in the /wp-content/uploads directory is symlinked to).
That way, hacker code has no chance of being uploaded to, writing to, and running within any core WordPress directories. An added benefit is that Pantheon’s Valhalla file system more efficiently serves up caching and images.
To give you further confidence that Pantheon can improve WooCommerce security, I can attest that I’ve had many sites on Pantheon.io since 2014 and none of them have ever been hacked. Not even the ones where clients had lax security practices and haven’t updated their sites in years!
2. Hide Your Dashboard
Making your dashboard invisible to hackers is a little-known path to improve WooCommerce security. The WordPress Dashboard URL is a well-known URL that hackers target regularly. Change your /wp-admin to anything else, the more obscure the better. There are plugins like Protect WP Admin that will manage this for you.
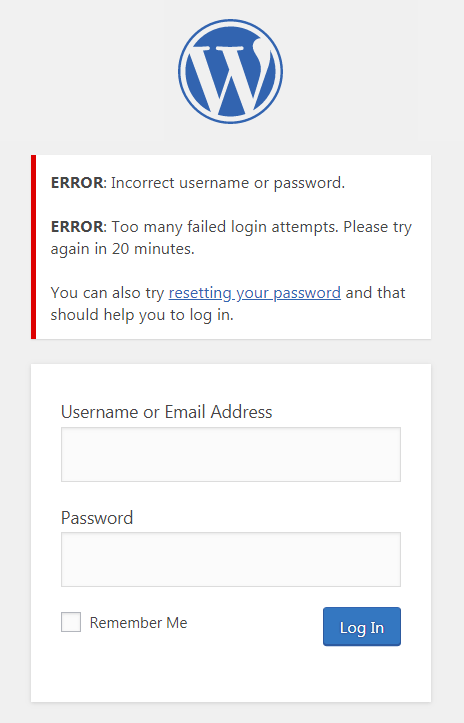
3. Limit Login Attempts
If for some reason you can’t or don’t want to protect your WP Admin and wp-login.php endpoints, then limit the number of times someone can attempt to log into your site. You’ll want to do this because hackers write automated scripts that repeatedly attempt commonly chosen username/password combinations. The Limit Login Attempts Reloaded plugin will allow you to customize how many attempts are allowed and to what extent you want to block people. It strikes a good balance between being helpful to people who genuinely forgot or mistyped their login information and being unhelpful to bots.
As noted above, hackers gain when you choose easily-guessed usernames and passwords. So, to improve WooCommerce security, don’t name your admin user “admin”. It’s also not advisable to use parts of your own name or website brand name (which can be derived from your blog author info or site name). Instead, pick an obscure name that is difficult to guess or brute-force attack.
4. Dump users who are no longer active
Delete users who are no longer on the site as an editor, contributor, or anything else other than a customer or a subscriber. If any Author, Editor, or Contributor users have created content, when you delete them there will be an option to assign their content to another username. You may want to review such content first to see if any rewrites are warranted due to first-person references in the copy.
5. Add a Security Plugin
Notice how adding a security plugin is the last item on the list of ways to improve WooCommerce security. That’s because you should be doing all the above options first so that the security plugin doesn’t have to work as hard. Or, maybe you won’t even need it at all. That’s a good thing!
There are multiple security plugins. WordFence is a popular option. Sucuri is another plugin that will help you filter out bad actors attacking your WooCommerce website as well. Sucuri’s malware detection and removal feature is a real lifesaver in the event that you do have a hacking event to deal with.
Another type of security plugin is one that enables two-factor authentication. Two-factor authentication relies on something you know (username and password) and something you have (a physical device) to ensure that you are you when you log in and not someone impersonating you. When you log in, you’re asked to also type in a quickly expiring code sent to your phone via a text message or an app. The “Two-Factor” WordPress plugin does a great job of this.
Bonus Tip
This tip kind of goes without saying: ALWAYS keep your site backed up and all the plugins, theme, and WordPress core files updated. If you’re no longer using a plugin or a theme, delete it. Plugins, theme, and core files that are not current or that are deactivated are some of the first things hackers will seek to exploit.
Summary
The quickest way to begin to improve WooCommerce security is to choose the best hosting you can find. Then, close off all the common hacker entry points like writable directories, login forms, and bad usernames and passwords. Get rid of inactive users with elevated permissions. Lastly, install a security plugin to scan for additional threats and malware, and be sure to keep your site software updated.
